Delft University of Technology
Delft University of Technology
Delft University of Technology
IEEE International Conference on Blockchain and Cryptocurrency 2025
In our paper, “Bitcoin Battle: Burning Bitcoin for Geopolitical Fun and Profit”, we uncover a tale of Bitcoin previously owned by Russian intelligence agencies being wielded and destroyed in a dark cyber operation.
Our research reveals how in 2022 over 7 Bitcoin (worth roughly $300,000 at the time) was intentionally made unspendable - or “burned” - through a Bitcoin feature called OP_RETURN. This wasn’t a mistake. We found evidence, hidden beneath the surface of the Bitcoin blockchain, showing that an unknown entity had seized control of wallets tied to GRU, FSB, and SVR - Russia’s elite intelligence services. In court documents and CTI reports these wallets are linked to infamous cyberattacks, like the 2016 hack of the U.S. Democratic National Committee and the 2020 SolarWinds breach.
But why burn the money? We believe it was a daring act — most probably by an adversary — to expose and sabotage Russia’s cyber efforts. Just days before Russia’s 2022 invasion of Ukraine, we observed hundreds of transactions burning Bitcoin, while others sent small amounts to Ukrainian forces, suggesting a geopolitical statement. We also traced these wallets to ransomware groups like Conti, hinting at a murky alliance between spies and cybercriminals.
Our study is one of the first to explore how nation-states exploit Bitcoin in cyber warfare. It shines a light on a hidden digital battlefield, where cryptocurrency becomes both a weapon and a target in global conflicts.
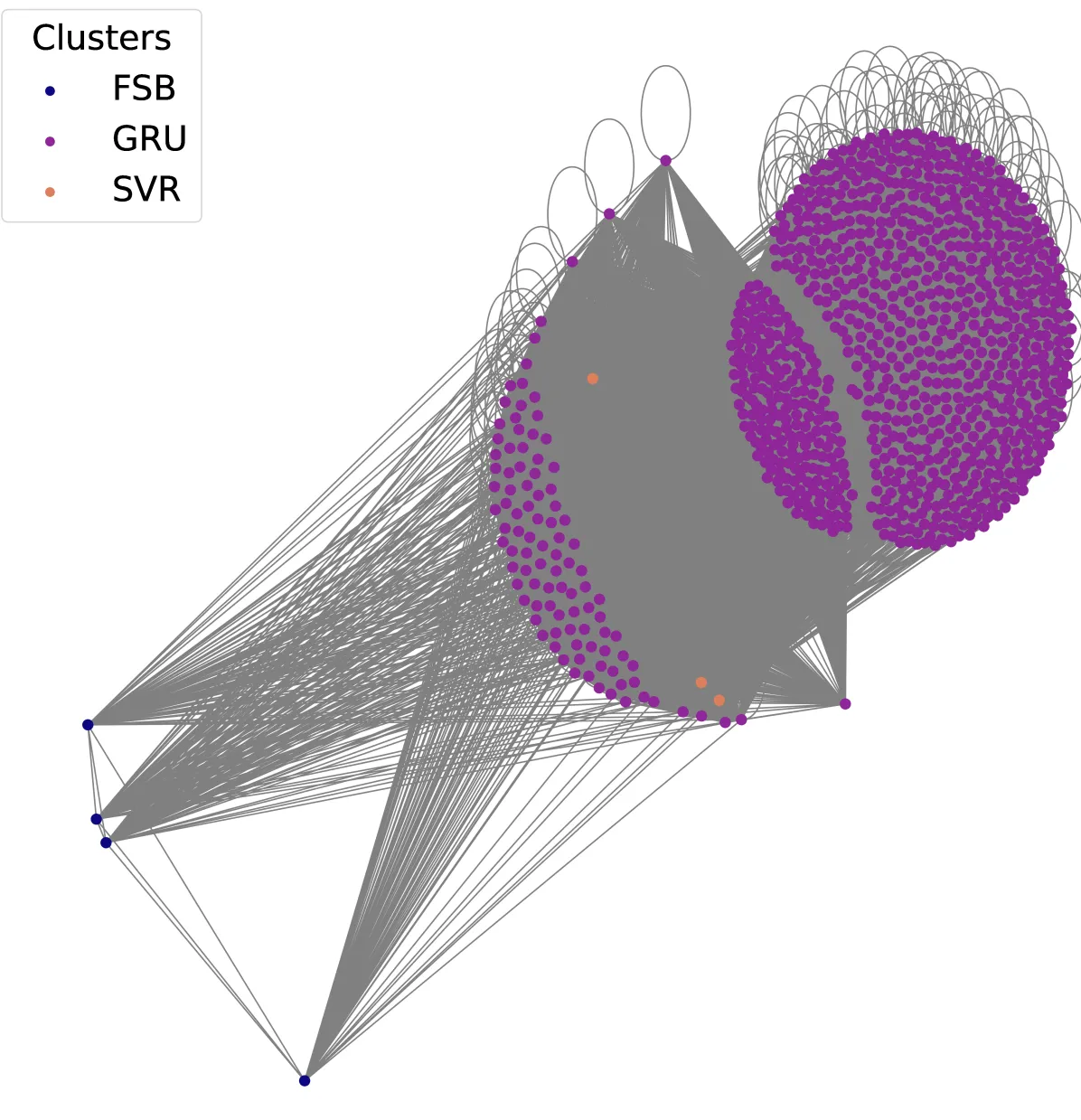
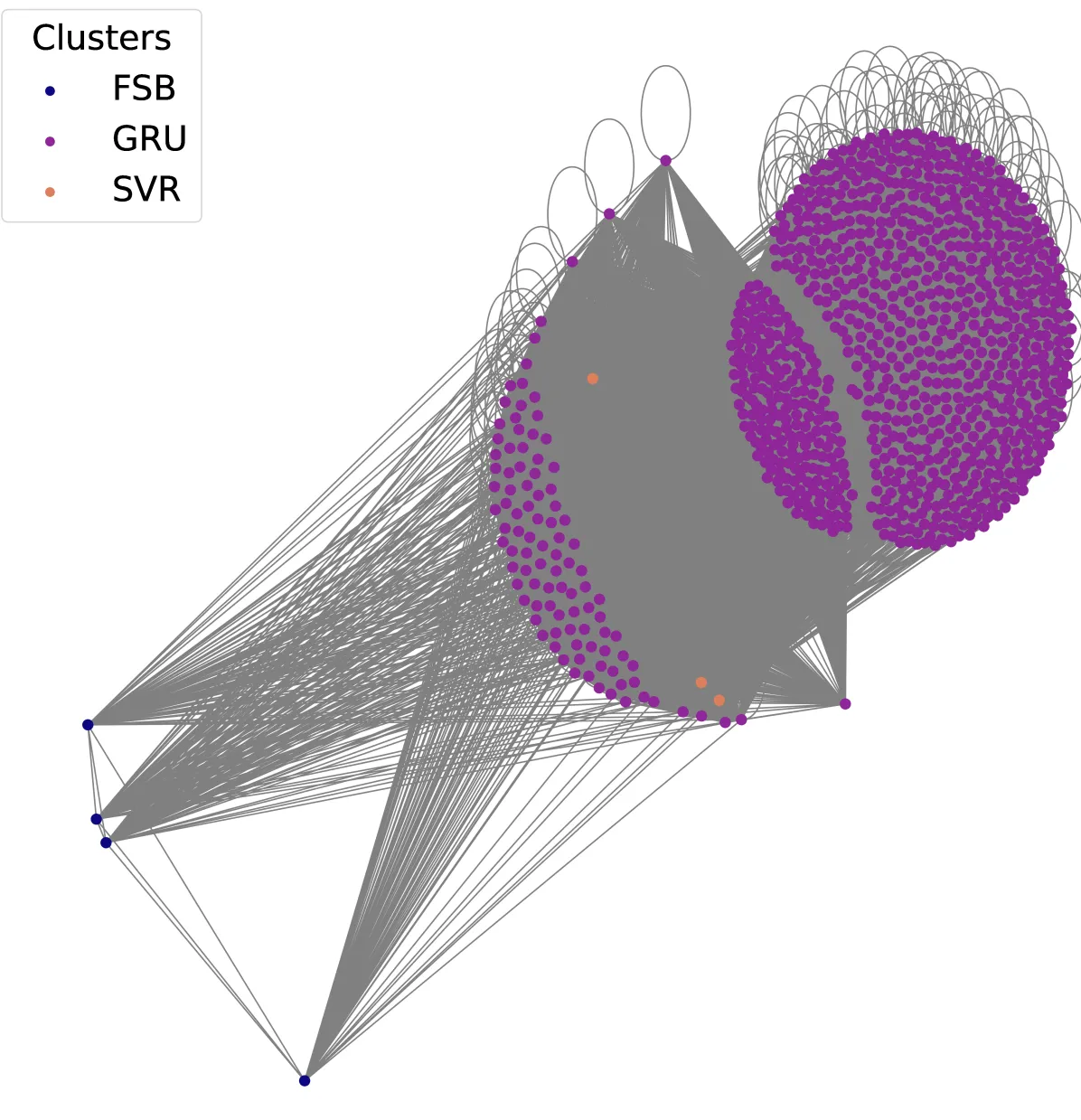
We employed a multi-faceted approach to analyze relevant Bitcoin transactions. We parsed all historical Bitcoin transactions up to August 1, 2024, from a Bitcoin Core full node (version 26.2), using the blockchain-parser library to extract OP_RETURN outputs from the nodes raw data files. These were processed into a DataFrame for efficient analysis on a high-memory workstation. We cross-verified transaction hashes with Blockchain.com’s API and used GraphSense for address clustering (via co-spending heuristics). The resulting dataset of 1,011 labeled GRU/FSB/SVR Bitcoin addresses is shared publicly for further research.
Based on our pre-analysis, we uncovered a striking anomaly in Bitcoin’s blockchain involving the OP_RETURN feature, which can permanently burn funds. When analyzed all historical OP_RETURN transactions up to August 1, 2024, pinpointed a surge of 583 OP_RETURN transactions on February 12, 2022, and 210 more on February 18 — just days before Russia’s invasion of Ukraine. These transactions burned over 7 Bitcoin, with messages in Cyrillic linking them to Russia’s GRU, FSB, and SVR intelligence agencies. Later, on March 14, we found 11 transactions donating to Ukraine’s armed forces, though without burning funds.
| OP_RETURN Message | English Translation | TXs | First TX | Last TX | Cuml. BTC Burn | Unique Addr. |
|---|---|---|---|---|---|---|
| ГРУ к ГРУ. Использованы для хакинга! | GRU to GRU. Used for hacking! | 505 | 2022-02-12 15:56:34 | 2022-02-18 23:25:24 | 6.15219839 | 222 |
| ГРУ к СВР. Использованы для хакинга! | GRU to SVR. Used for hacking! | 309 | 2022-02-12 15:56:34 | 2022-02-18 21:41:59 | 0.90929650 | 196 |
| ГРУ к ФСБ. ИспользоЂаны для хакинга! | GRU to FSB. Used for hacking! | 248 | 2022-02-12 15:56:34 | 2022-02-18 23:25:24 | 0.00006946 | 161 |
| Помощь Украину с деньгами от ГРУ хакиров | Helping Ukraine with money from GRU hackers | 54 | 2022-03-14 18:14:13 | 2022-03-14 19:25:15 | 0 | 54 |
In Section V of our paper, we investigate the ownership of Bitcoin wallets involved in the OP_RETURN campaign, aiming to attribute them using public evidence. We identified 986 addresses, with three tied to Russian intelligence: one from the 2016 DNC hack (GRU’s Fancy Bear and SVR’s Cozy Bear) and two from the 2020 SolarWinds breach (SVR’s APT-29), per court and CTI sources.
| Entity | # addresses | # clusters | Cluster size (avg) | Cluster size (std) | # transactions (avg) | # transactions (std) |
|---|---|---|---|---|---|---|
| SVR | 3 | 3 | 1.000000 | 0.000000 | 1.666667 | 0.471405 |
| GRU | 15,856 | 872 | 16.196118 | 57.489070 | 13.371560 | 31.313955 |
| FSB | 13 | 4 | 3.250000 | 2.277608 | 204.250000 | 2.277608 |
These wallets burned 7.06 Bitcoin, with OP_RETURN messages like “GRU to SVR” indicating GRU origins and SVR/FSB outputs. Using co-spending clustering, we grouped them into 879 clusters — 15,856 GRU addresses, 3 SVR, and 13 FSB — showing distinct agency control. Most were legacy addresses, hinting at older software, and one GRU wallet later linked to Conti ransomware. We conclude Russian agencies initially owned these, but an outsider or insider likely seized the keys, exposing their use.
In Section VI, we analyze the financial transactions of the OP_RETURN campaign tied to Russian intelligence. We found 1 Bitcoin funded the effort via Cryptomixer.io on February 1, 2022, enabling subsequent activity.
Between February 12-18, 2022, fractional payments — often under $1 — flowed to GRU, SVR, and FSB wallets, with one transaction splitting into 880 outputs worth $1,424.09 total, and another burning 0.966 BTC. On March 14, 11 transactions sent $975.92 to Ukraine’s forces with no burns, tagged “Helping Ukraine with money from GRU hackers.” Post-2022, a GRU wallet sent funds to Conti ($466.59), Rain.com ($229.05), and Reisbet. We estimate over $300,000 was burned, suggesting a strategic act beyond profit, using mixers and small transfers to obscure and disrupt.
| Label | Total Transactions | Total Value (USD) | Mean Value (USD) | Median Value (USD) | Min Value (USD) | Max Value (USD) | Outlier Count | Outlier Mean (USD) | Outlier Min (USD) | Outlier Max (USD) |
|---|---|---|---|---|---|---|---|---|---|---|
| FSB | 308 | 129.20 | 0.42 | 0.43 | 0.22 | 0.43 | 16 | 0.23 | 0.22 | 0.25 |
| GRU | 59,855 | 2,065,728.28 | 34.51 | 0.43 | 0.22 | 8,353.29 | 864 | 1,995.44 | 835.53 | 8,353.29 |
| SVR | 1,083 | 336.72 | 0.31 | 0.22 | 0.22 | 0.43 | 0 | 0.00 | 0.00 | 0.00 |
We determine that the OP_RETURN campaign reflects a calculated act of denial and destruction within the Russo-Ukrainian conflict, executed by an actor who opted to destroy significant value rather than profit. This choice, alongside the use of mixers, suggests a sophisticated effort to disrupt rather than enrich, positioning Bitcoin as both a tool and a target in cyber warfare. Our findings prompt further inquiry into the origin of this campaign, as well as the strategic motives at play.
Please read our full paper for the entire analysis. Certain aspects of our analysis have previously been highlighted in a blogpost by Chainalysis, but our work extends their analysis.
The authors would like to express their gratitude to Bernhard Haslhofer of Iknaio for providing access to the GraphSense API, which allowed Bitcoin address clustering and also to Scorechain, which facilitated the identification of potential ownership of addresses. This work was supported by the European Commission under the Horizon Europe Programme as part of the project SafeHorizon (Grant Agreement #101168562). The content of this article does not reflect the official opinion of the European Union. Responsibility for the information and views expressed therein lies entirely with the authors.
@misc{bitcoinbattle,
title={Bitcoin Battle: Burning Bitcoin for Geopolitical Fun and Profit},
author={Kris Oosthoek and Kelvin Lubbertsen and Georgios Smaragdakis},
year={2025},
eprint={2503.13052},
archivePrefix={arXiv},
primaryClass={cs.CR},
url={https://arxiv.org/abs/2503.13052},
}